AI is powerful. The field is moving fast.
How do you stay on top?
The tools are changing fast, the accuracy question is real, and healthy skepticism makes sense. But the capabilities are compounding quickly and teams investing are already building workflows and institutional knowledge that will be hard to catch up to later. Waiting has its own cost.
Wire up a general-purpose model and write custom tooling around it. Maintain the pipeline as APIs change underneath you. This works, but you'll spend months building and maintaining infrastructure instead of doing actual analysis.
Ask a question. Get an answer backed by evidence. Verify what matters. Move on. Sidekick is purpose-built for binary analysis — already integrated, verifying, and improving on hard targets. You stay focused on the analysis, not the tooling.
Find what matters.
Point Sidekick at a binary and ask what you need to know. Semantic search finds relevant code even when names are stripped, strings are sparse, and the answer is spread across a dozen functions. You're triaging in minutes, not hours.
See how search works →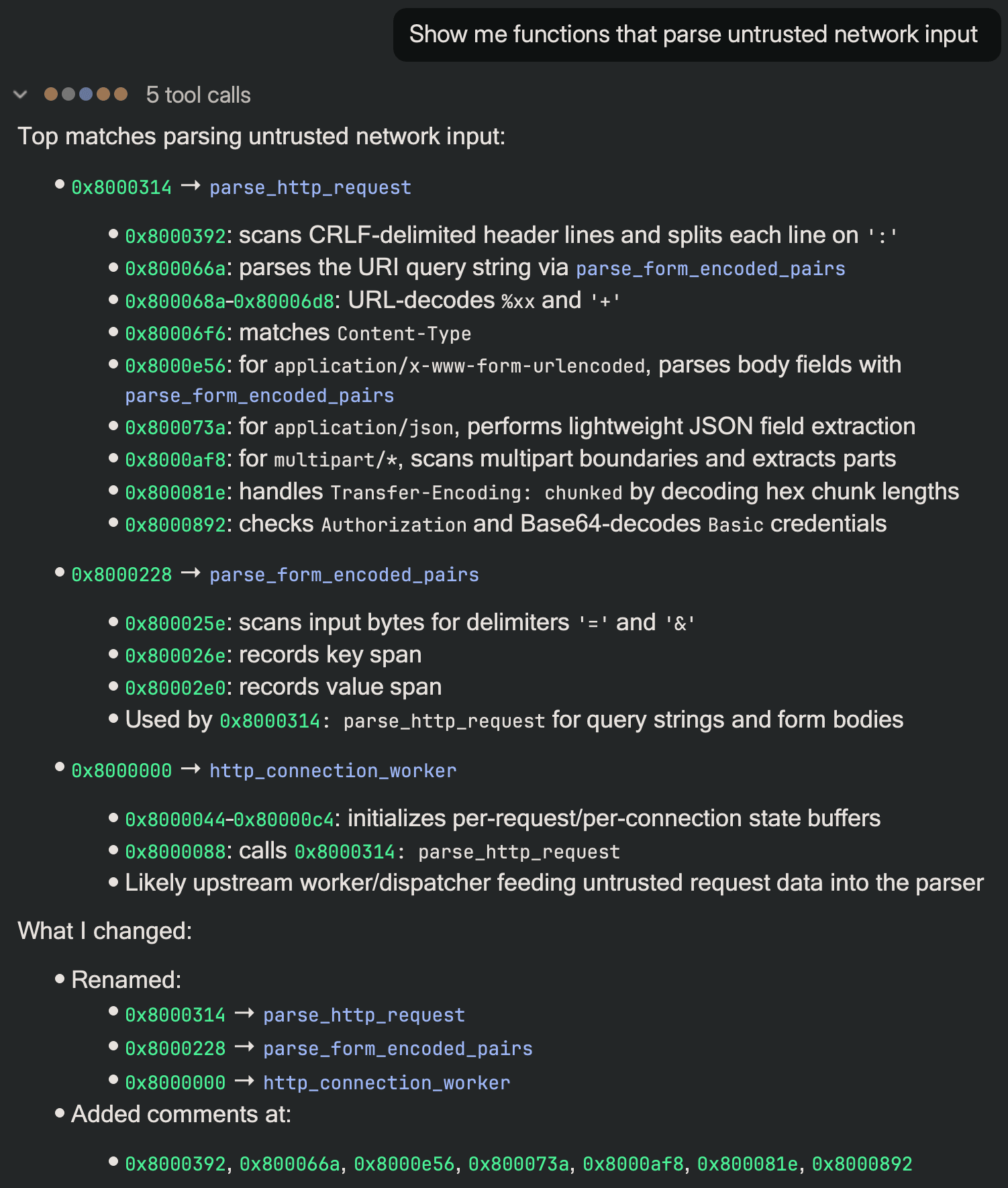
Make it understandable.
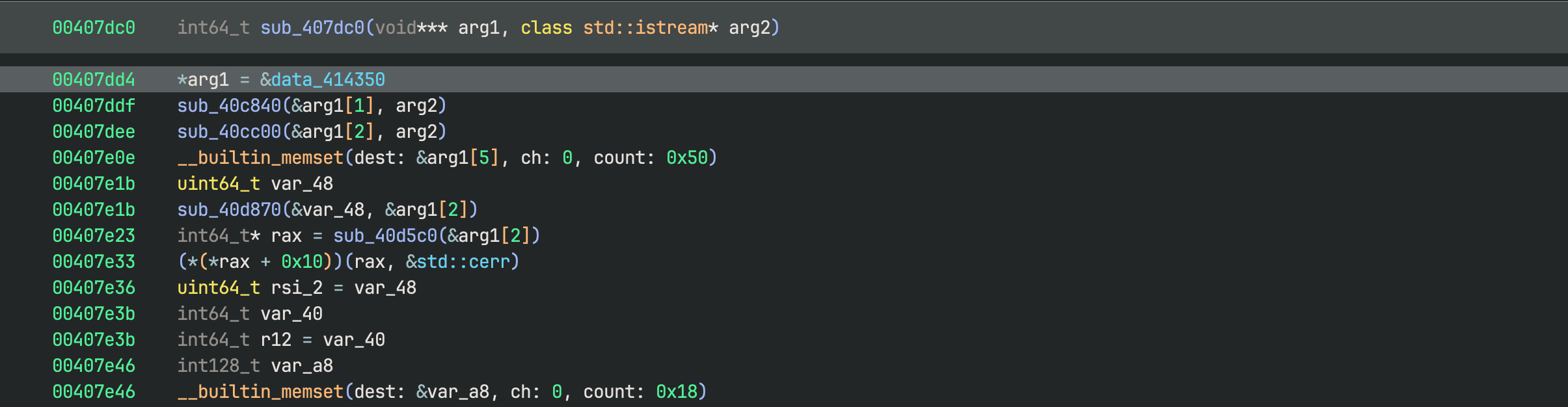
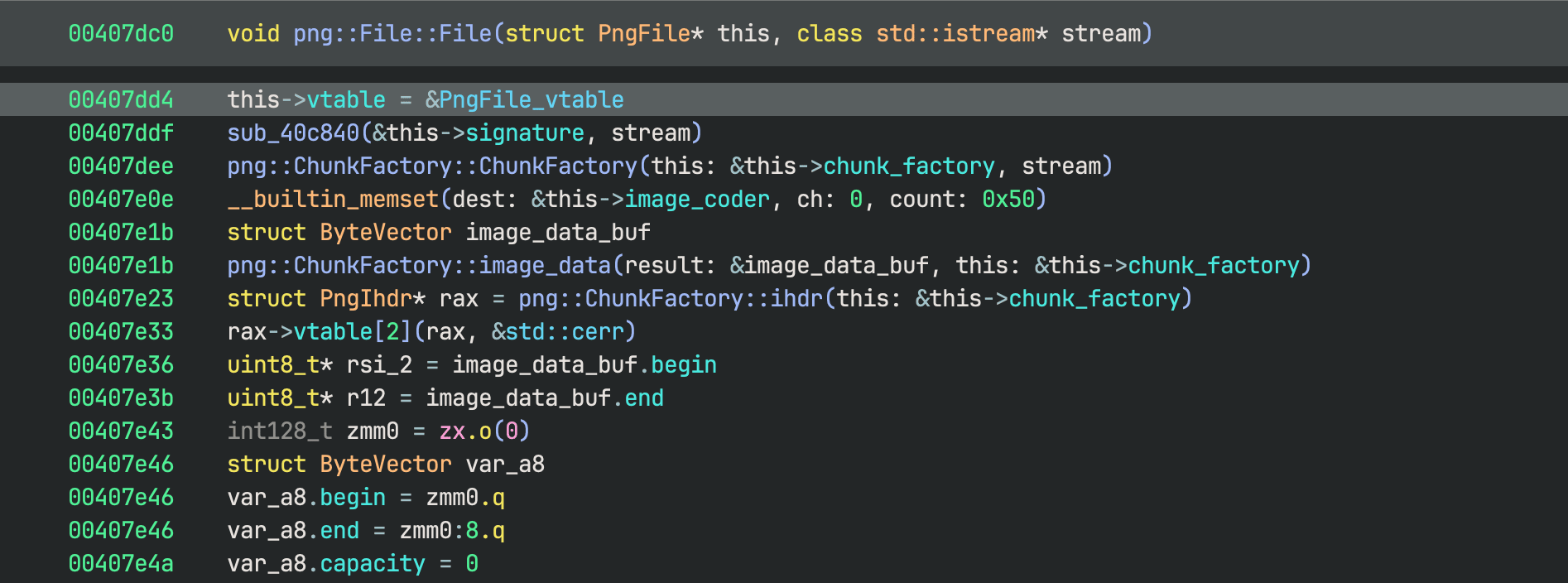
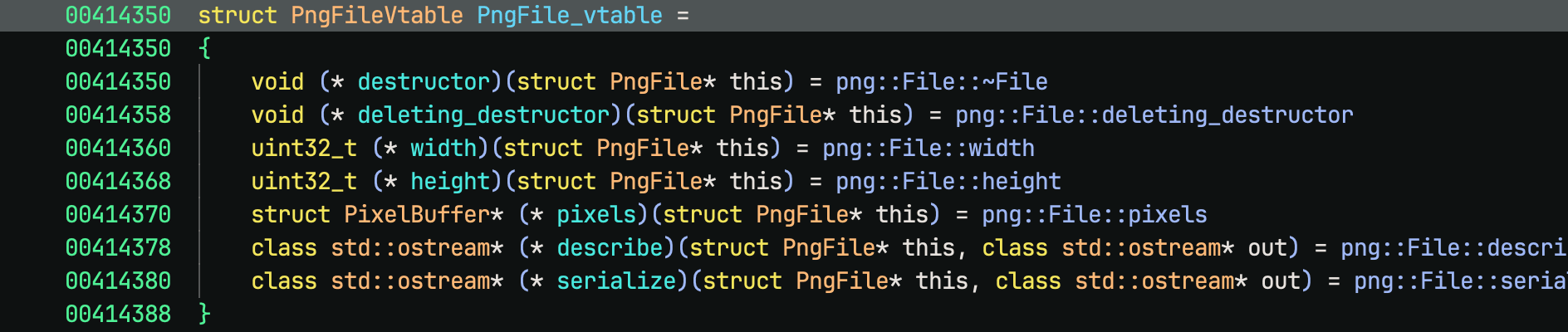
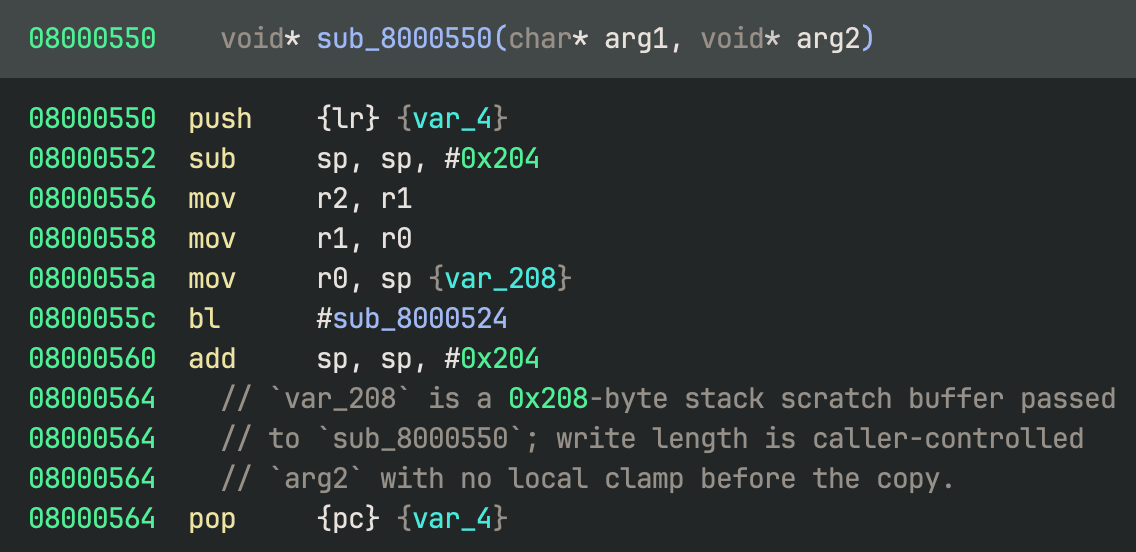
Sidekick recovers types, names, and structures from stripped and obfuscated binaries. When the decompiler gets something wrong, such as a bad type propagation, collapsed control flow, or misread calling conventions, Sidekick catches it and repairs it. You read the decompilation like annotated source and focus on the analysis.
Extract what you need.
Sidekick produces the artifacts to support your workflows. Findings accumulate in a notebook that persists across sessions with evidence links intact. When it's time to hand off or write the report, the work is already organized.
See the analysis notebook →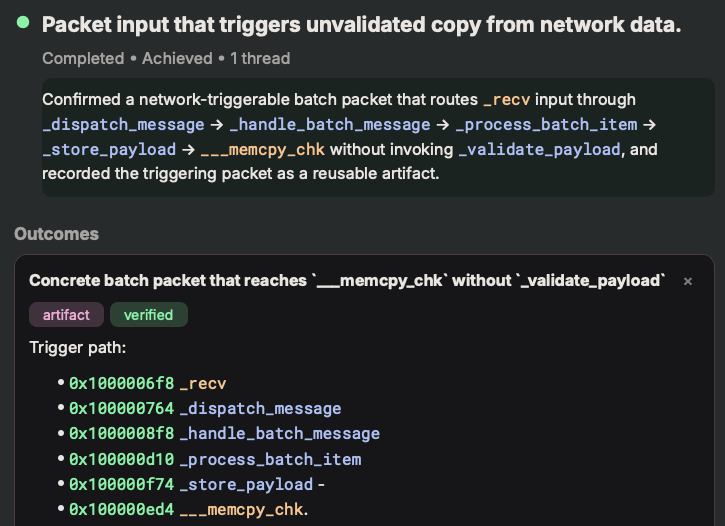
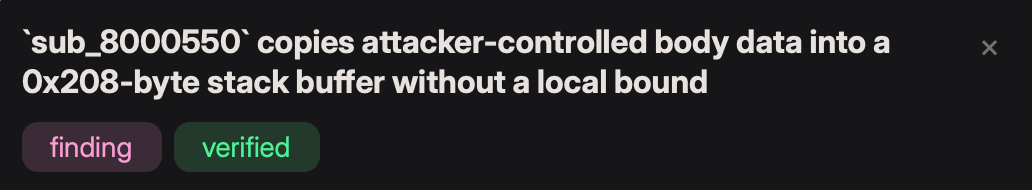
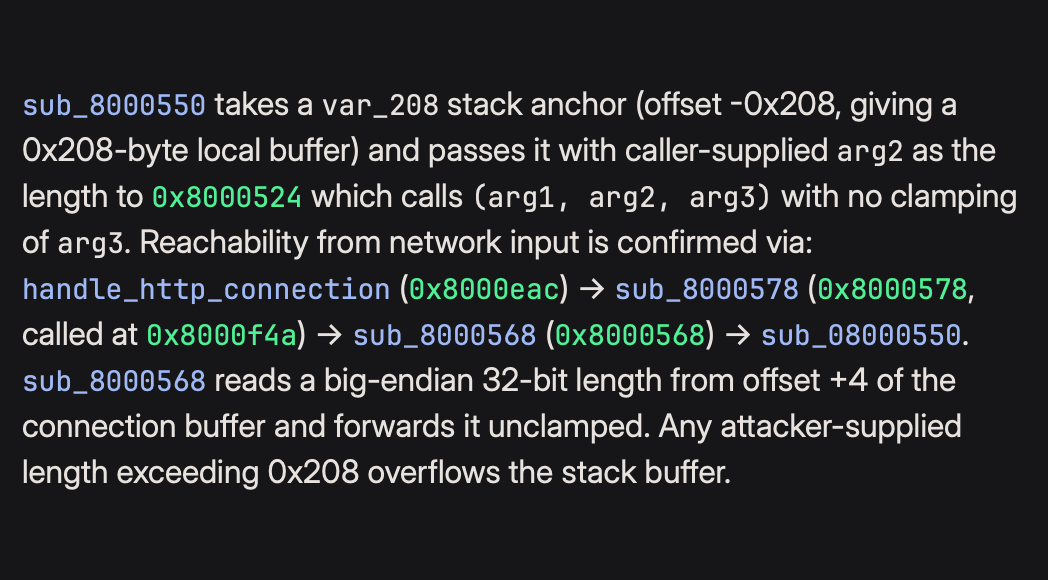
Analysis that cross-examines itself.
Every claim Sidekick produces links to IL, assembly, or memory. A background validation agent checks findings to catch type misrecovery, calling convention errors, and conditions that haven't been tested. When it finds a problem, it remediates and flags the finding.
Findings carry their status: draft, verified, or rejected. You see the full reasoning trail.
See how verification works →- Verified
- Rejected
Inside your decompiler, not beside it.
Sidekick lives in Binary Ninja alongside your analysis database. In every interaction, every function name is a link and every finding navigates to the relevant addresses. No copy-pasting between a chat window and your tools.
We do the work so you don't have to.
You don't know where AI will fail on a binary until you try. So we try first. We run our own prioritized binary analysis pipeline against hard targets, specifically to find where the tools break. We fix what we find, and the improvements ship to every Sidekick user.
The result: Sidekick carries specialized knowledge about compiler quirks, platform-specific calling conventions, decompiler failure modes, and obfuscation techniques. We work to preventively find issues, diagnose them, and build solutions for them.
Automate your analysis pipeline.
Sidekick is scriptable. Write Python that invokes agents so that you can run a vulnerability pattern across a firmware library, apply a check to every function, or chain agents together. Use the API to embed Sidekick in pipelines where no human is present until the results demand attention.
See how automation works →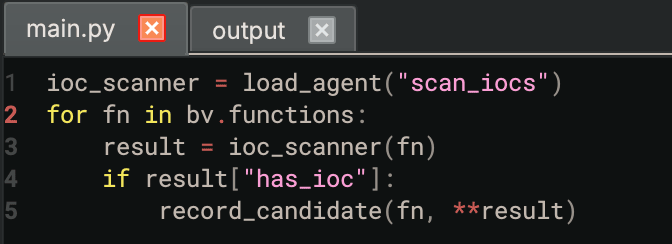
In the cloud or on-premises.
Start immediately in our managed cloud, or deploy fully on-premises when binaries can't leave your network, protecting your proprietary information.
Learn More