Extract what you need.
Can it produce the deliverables my job requires?
The problem
The analysis is in your head or scattered across chat logs. Reproducing findings takes almost as long as the original analysis. Handoff to teammates loses context. When the report is due, you're reassembling work instead of writing conclusions.
How Sidekick surfaces
Findings accumulate in a persistent notebook. Every finding carries its verification status and evidence links. The notebook survives across sessions so that you can pick up where you left off or export when you're ready to hand off to a teammate.
Sidekick does not just keep the answer in chat. When an investigation turns up something reusable — a sink path, a bypass condition, a concrete trigger packet, an IOC list, a vulnerability assessment — you can have Sidekick record it as a linked notebook artifact tied back to the binary.
Worked example
You are hunting for a validation bypass in a packet parser.
Ask Sidekick to find a path from recv to a data sink like memcpy where attacker-controlled
input stays reachable without passing through the validation function.
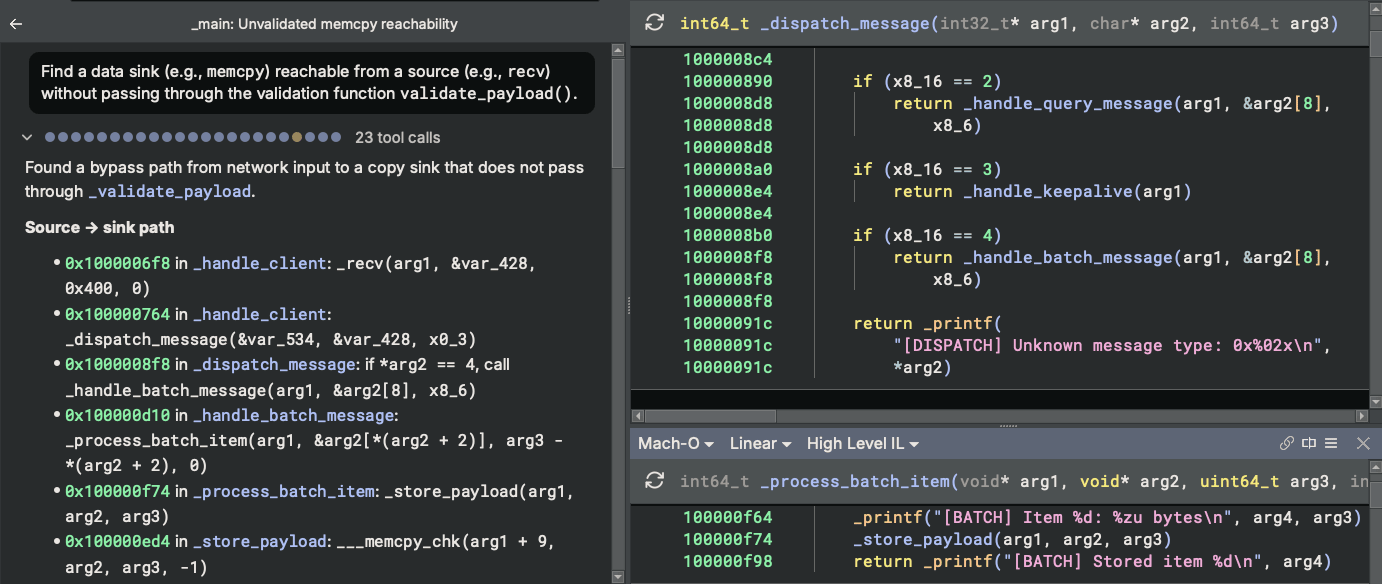
recv-to-memcpy path is surfaced with the bypass condition identified.
Ask Sidekick to record the concrete input packet needed to trigger the discovered behavior.
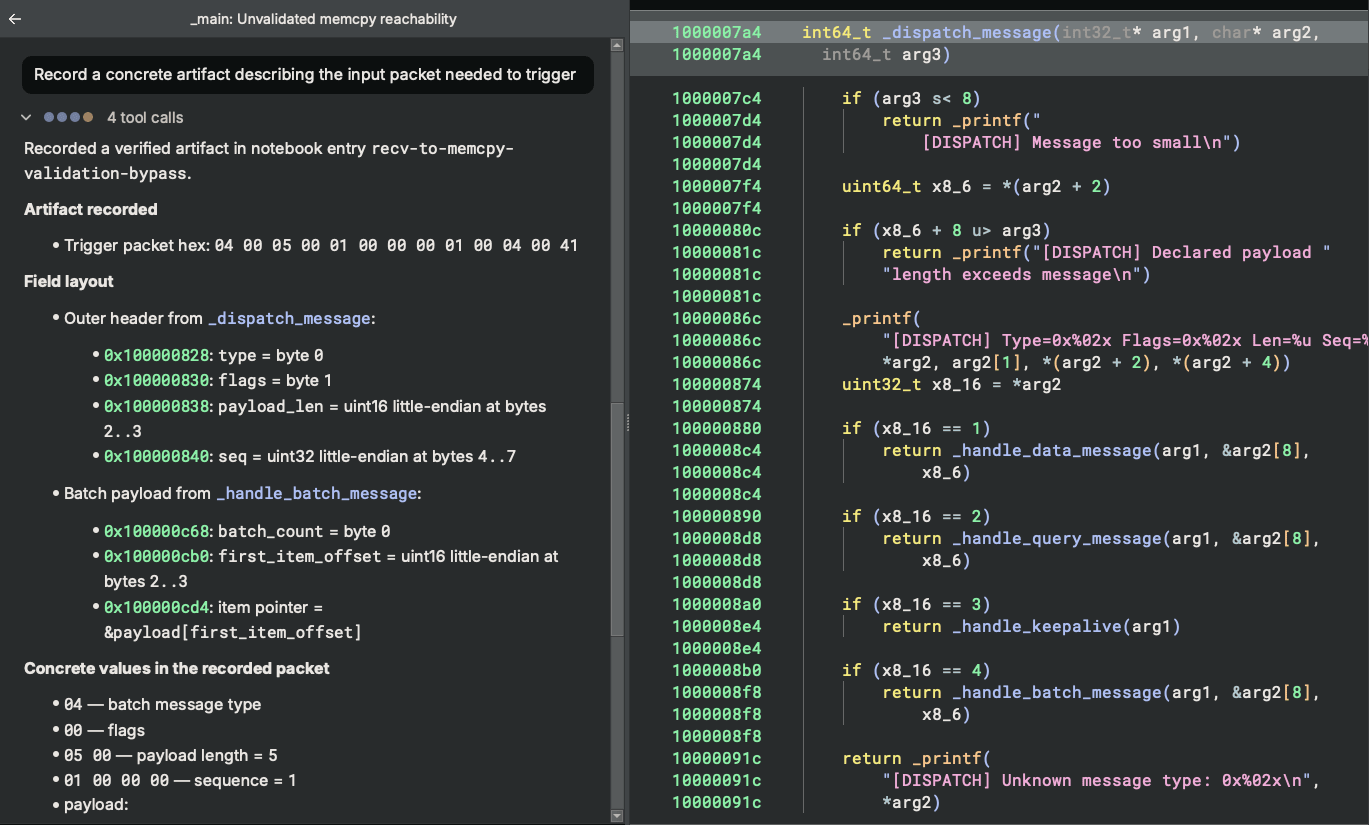
The notebook captures the packet bytes, field layout, and replay assumptions so another analyst can pick it up immediately.
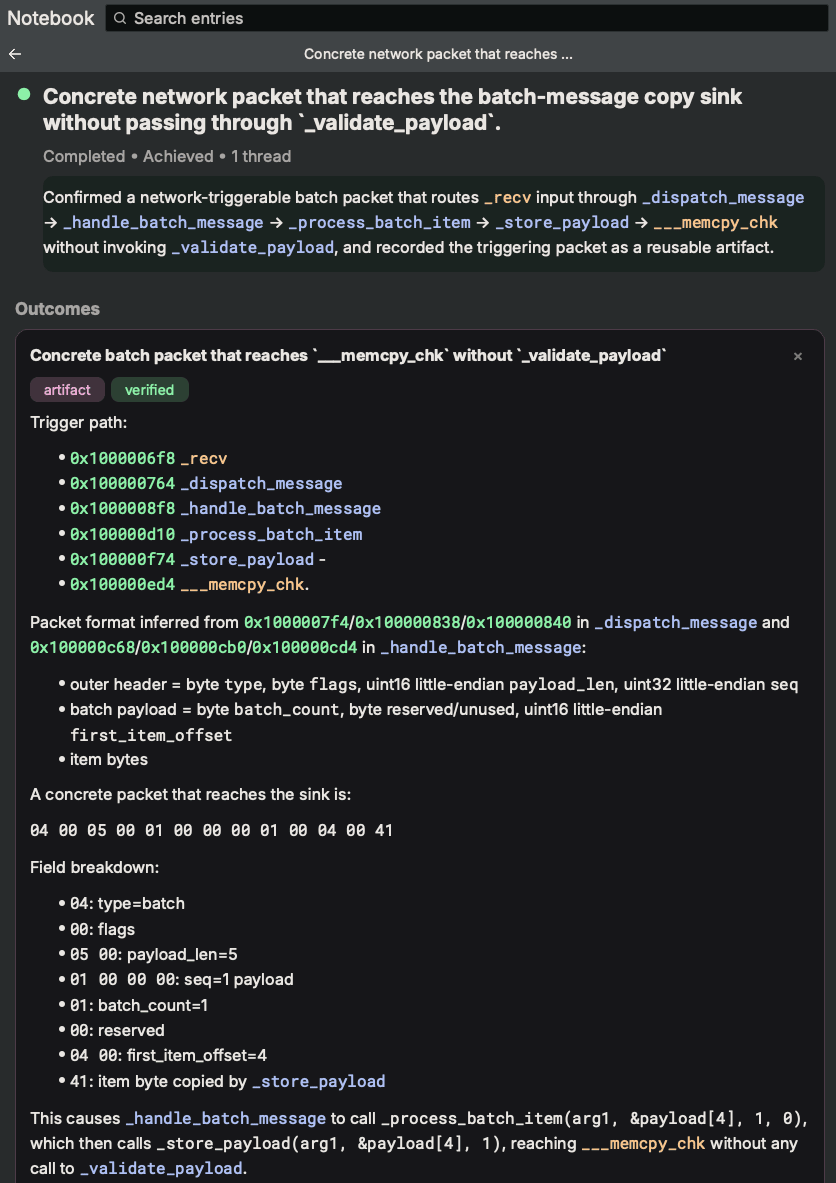
What you get
Organized findings, evidence links, verification status, and concrete artifacts such as trigger packets or replay conditions. When it's time to report, reproduce, or hand off the work, your answers and the reasoning behind them are already preserved.